There have been a number of small business that have been getting ripped of through fraudulent wire transfers. In one example, Krebs on Security covers the details of how an IT consulting firm lost nearly $100,000 through wire transfers it did not make.
Customers need to make sure that their banks are using robust authentication, not just static passwords with additional questions to verify identity. These are too easily captured by keyboard loggers or other spoofing devices. The banks need to employ multi-factor authentication that cannot be victimized by the malware that is rampant throughout corporate America.
In addition, companies should be looking into keyboard encryption for computers that are accessing sensitive information. Please reach out if you would like to learn about how to defend you and your business.
Tips on Improving IT Security and System Administration from Castle Ventures Corporation.
Tuesday, February 23, 2010
Tuesday, February 16, 2010
Adobe Patches Reader and Acrobat Again
Security issues continue to crop up in Adobe Reader and Acrobat. Adobe has issued patches for Reader and Acrobat to correct security issues. Users should upgrade to version 9.3.1 of the software. Click here to see the Security Bulletin.
Saturday, February 13, 2010
Fatal System Error
We read every day about Eastern European crime syndicates that are involved in cybercrime, cyberwarfare, and other nefarious activities on the Internet. In many ways these organizations are block boxes, with very little information reported on who they are and how they work. Joseph Menn in his new book, “Fatal System Error,” tells the stories of two individuals, Barrett Lyon and Andrew Crocker, who have gone toe-to-toe with the evil hackers of the East. Menn has created a thrilling and informative work that delves into the specifics of these two Internet heroes.
The book starts off telling the story of a young self-taught computer whiz named Barrett Lyon. Barrett becomes an expert in fighting off Denial of Service attacks. For those looking for an in-depth technical discussion of how Barrett wards off the attacks you will need to search elsewhere. The specific approaches that Prolexic takes are not described here; which in entirely appropriate in the context of how this story is told. Most of Barrett’s initial clients were in the Internet gambling business and were located out of the United States. He founds a company, Prolexic to provide a secure hosting environment to protect his clients from the Distributed Denial of Services attacks. Unfortunately for Barrett, the politics involved in running Prolexic get in the way of its mission and he decides to move on.
One of the main goals of the attackers was to extort money from the gambling sites. After many episodes of defending against the numerous extortion attempts Barrett tries to fight back. He contacts the FBI on many occasions, without much success. However, in researching the attacks on BetCRIS, one of clients, he gets the involvement of Andrew Crocker of England’s National Hi-Tech Crime Unit.
Menn expertly transitions the story to tales of Andrew Crocker. Crocker’s goal is to identity the criminals in Russia and bring them to justice. In the telling of this story, Menn sheds significant light on to why convicted these foes is such a challenge. At the core of the problem is that the Russian government does not want these people prosecuted. On the local level bribes of police and judicial employees keep the criminals out of jail. At the national level the criminal masterminds are protected by high-level operatives in the Russian government. They touch on the periphery of the Russian Business Network and speculate that the Russian government overlooks the illegal activities of these groups because they want to use this expertise to support political aims such as the suppression of dissent and information in places such as Georgia and Estonia.
One of the conclusions that Menn and the investigators come to is that the protocols of the Internet need to be redesigned. They were developed by the US government to build a distributed, resilient network, as which they have been an enormous success. The protocols were not developed with security in mind; it was not a consideration 35 years ago. Policing the Internet with current policies is extremely difficult if not impossible because the countries of the world have different objectives and place different emphasis on these crimes.
If you want a look into the Belly of the Beast, Fatal System Error
, is a great place to start.
The book starts off telling the story of a young self-taught computer whiz named Barrett Lyon. Barrett becomes an expert in fighting off Denial of Service attacks. For those looking for an in-depth technical discussion of how Barrett wards off the attacks you will need to search elsewhere. The specific approaches that Prolexic takes are not described here; which in entirely appropriate in the context of how this story is told. Most of Barrett’s initial clients were in the Internet gambling business and were located out of the United States. He founds a company, Prolexic to provide a secure hosting environment to protect his clients from the Distributed Denial of Services attacks. Unfortunately for Barrett, the politics involved in running Prolexic get in the way of its mission and he decides to move on.
One of the main goals of the attackers was to extort money from the gambling sites. After many episodes of defending against the numerous extortion attempts Barrett tries to fight back. He contacts the FBI on many occasions, without much success. However, in researching the attacks on BetCRIS, one of clients, he gets the involvement of Andrew Crocker of England’s National Hi-Tech Crime Unit.
Menn expertly transitions the story to tales of Andrew Crocker. Crocker’s goal is to identity the criminals in Russia and bring them to justice. In the telling of this story, Menn sheds significant light on to why convicted these foes is such a challenge. At the core of the problem is that the Russian government does not want these people prosecuted. On the local level bribes of police and judicial employees keep the criminals out of jail. At the national level the criminal masterminds are protected by high-level operatives in the Russian government. They touch on the periphery of the Russian Business Network and speculate that the Russian government overlooks the illegal activities of these groups because they want to use this expertise to support political aims such as the suppression of dissent and information in places such as Georgia and Estonia.
One of the conclusions that Menn and the investigators come to is that the protocols of the Internet need to be redesigned. They were developed by the US government to build a distributed, resilient network, as which they have been an enormous success. The protocols were not developed with security in mind; it was not a consideration 35 years ago. Policing the Internet with current policies is extremely difficult if not impossible because the countries of the world have different objectives and place different emphasis on these crimes.
If you want a look into the Belly of the Beast, Fatal System Error
, is a great place to start.
Monday, February 8, 2010
Updating Varonis DA Immediately
Varonis DatAdvantage updates the Work Area's File Permissions and User Information on a nightly basis. Sometimes, after performing significant changes to improve your security you want to get a view of the current state your server. To do that you need to run the nightly jobs. You can run those jobs manually in two ways. One is through the Configuration menu with the DA GUI. The other, which I prefer, is to go directly to the SQL Management Studio to perform the jobs so I can monitor their progress.
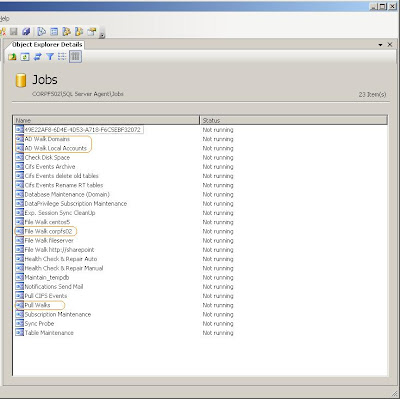
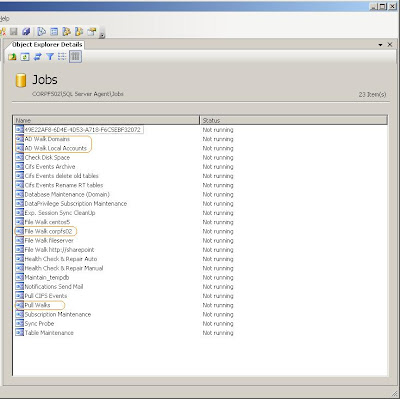
Here are the steps:
1) Run the AD Walk(s)
2) Run the File Walk for each server that you have updated.
3) When those jobs are finished run the Pull Walk.
After the Pull Walk is complete, you can restart the DatAdvantage UI and the permissions will be current.
Sunday, February 7, 2010
Harden Your Service Accounts
In many cases we have service accounts that need powerful privileges to perform their tasks. This power also means that there is an elevated level of risk associanted with these accounts. They could be used inappropriately to access resources without accountability, since they are not tied directly to a person. There are two steps that I recommend that people follow in locking fown these accounts. Both of these activities involve starting Active Directory Users and Groups and then selecting the Properties options on the selected service acccout. First, select the Terminal Services Profile and check the option to Deny this user permissions to log on to any Terminal Server. The screen shot is listed here:

 Then we want to restrict the computers that the service account cal log into. This is found on the Account tab. Once on this tab, click on the Log On To command button. At this point enter the computer name(s) where the service account is used. This will limit the account to logging into only this machine.
Then we want to restrict the computers that the service account cal log into. This is found on the Account tab. Once on this tab, click on the Log On To command button. At this point enter the computer name(s) where the service account is used. This will limit the account to logging into only this machine.

Subscribe to:
Comments (Atom)